Platform

Tanay Rai

Third-party cyber risk in the banking sector has evolved far beyond traditional vendor review processes. Modern banks operate within highly interconnected digital ecosystems involving fintech providers, cloud infrastructure vendors, payment processors, credit scoring platforms, fraud detection systems, and regulatory reporting tools.
These third-party services are now deeply embedded in critical financial workflows, including identity verification, transaction processing, settlement systems, digital banking platforms, and regulatory compliance reporting.
As a result, cybersecurity risk in banking is no longer confined to the internal IT environment. Instead, it exists across a distributed network of external providers whose vulnerabilities can directly affect financial institutions.
In this environment, third-party cyber risk is no longer simply a documentation or compliance challenge. It has become an operational exposure that spans the entire financial ecosystem.
The Expansion of the Third-Party Attack Surface in Banking.
Modern banking infrastructure depends heavily on external technology providers. Banks integrate a wide range of third-party services, including:
Fintech APIs supporting Open Banking and financial innovation
Cloud infrastructure platforms hosting digital banking services
Payment gateways and transaction processing networks
Customer identity verification services (KYC / AML platforms)
Fraud detection and risk analytics platforms
Data aggregation and credit scoring providers
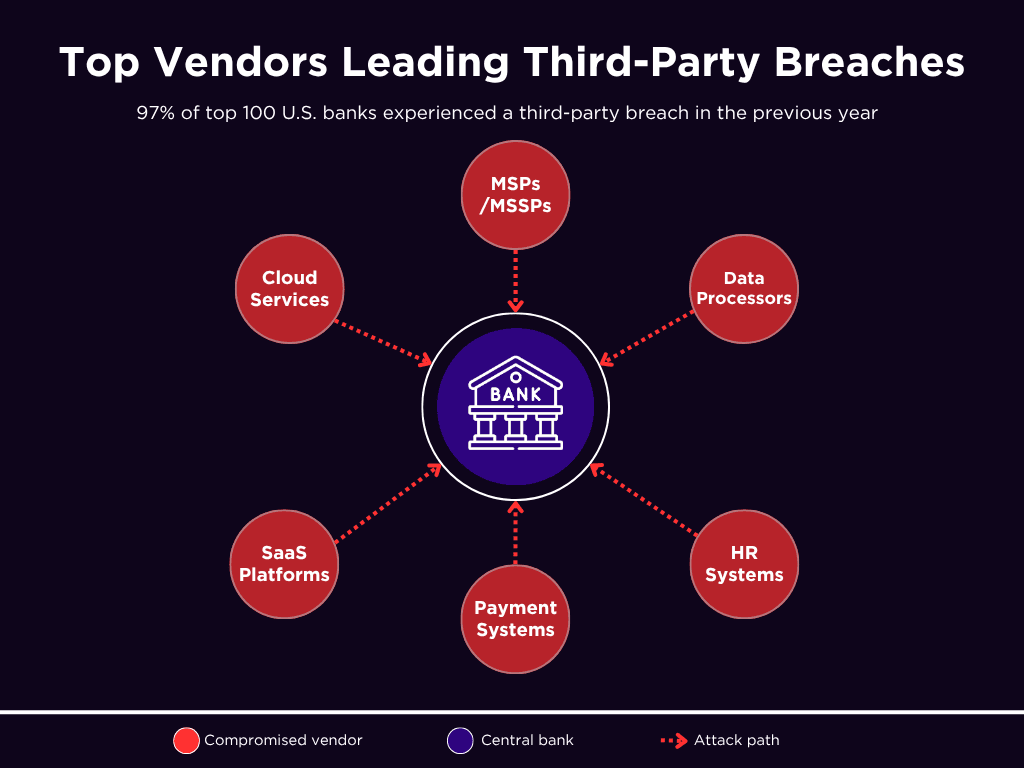
These services sit directly within critical banking processes, including authentication, transaction authorization, data exchange, and regulatory reporting.
This architecture significantly expands the cyberattack surface.
Instead of targeting individual banks directly, attackers increasingly exploit vulnerabilities within widely used technology providers that support multiple financial institutions.
Several incidents illustrate this shift:
1. Evolve Bank & Trust Fintech Breach
A cyberattack on Evolve Bank & Trust exposed sensitive data across multiple fintech platforms relying on its banking-as-a-service infrastructure, demonstrating how a compromise at a single provider can affect many financial institutions.
2. Truist Bank Third-Party Vendor Breach
Customer data was exposed following a breach at Financial Business and Consumer Solutions (FBCS), a debt-collection vendor working with Truist Bank, underscoring the risks of outsourced financial services.
3. Marquis Software Solutions Fintech Vendor Attack
A ransomware attack on Marquis Software Solutions, a technology vendor serving hundreds of banks and credit unions, compromised data for approximately 788,000 banking customers, underscoring the systemic risk posed by shared financial technology providers.
These incidents demonstrate a key reality: attackers increasingly target shared technology dependencies within the financial ecosystem rather than individual banks.
Why Traditional Vendor Risk Management Fails in Banking.
Traditional Third-Party Risk Management (TPRM) models were designed for slower technology environments.
Banks historically relied on:
Vendor security questionnaires
SOC reports and audit attestations
Annual risk assessments
Contractual compliance declarations
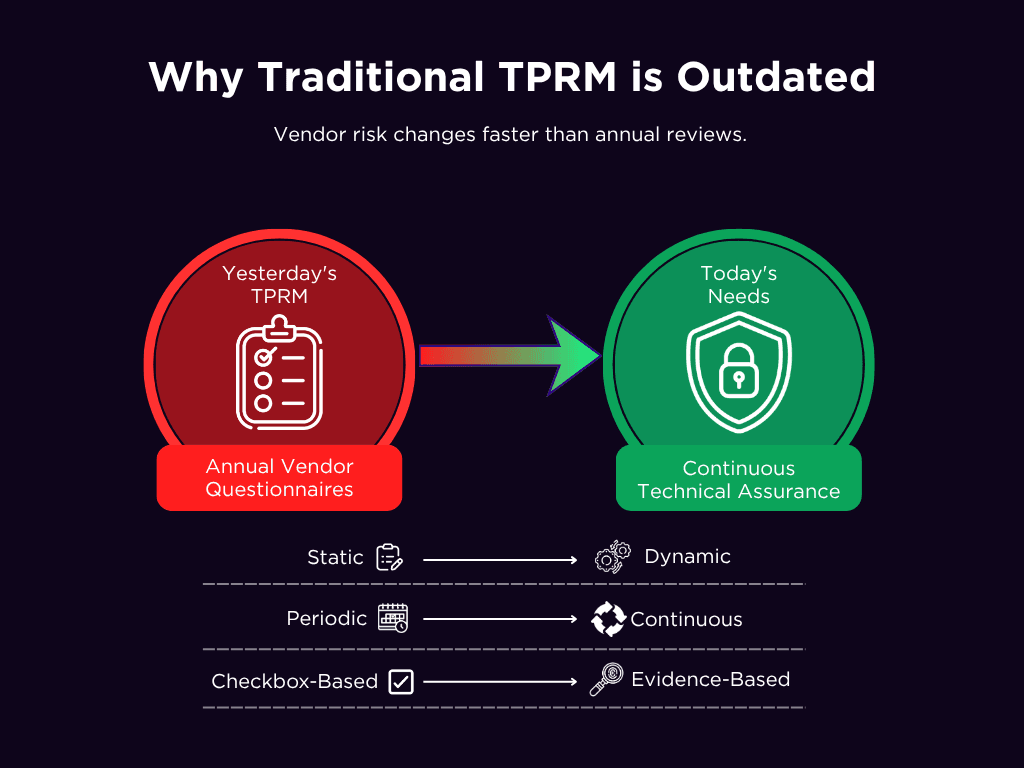
While these controls once provided reasonable assurance, they struggle to keep pace with modern banking ecosystems.
Technology environments now evolve rapidly. Vendors frequently introduce new APIs, deploy new infrastructure, onboard subcontractors, or modify identity management systems.
A vendor that passed a risk review six months ago may now expose new risks, such as:
Newly exposed administrative interfaces
Weak identity access controls
Vulnerable internet-facing infrastructure
Changes in cloud configurations
Newly introduced third-party subprocessors
The challenge is not merely a lack of documentation but the short lifespan of security evidence. By the time assessments are completed, the vendor’s environment may already have changed.
As a result, the discipline of TPRM in banking is shifting from static compliance verification toward continuous technical assurance.
The Framework Shift Toward Ecosystem Security.
Regulatory frameworks governing financial institutions increasingly treat third-party risk as a core operational resilience issue.
Digital Operational Resilience Act (DORA)
DORA requires financial institutions to manage ICT third-party dependencies through structured governance mechanisms. These include:
Identification of critical technology providers
Monitoring subcontracting relationships
Testing operational resilience scenarios
Managing concentration risk
Establishing exit strategies for critical providers
NIS2 Directive
NIS2 extends supply-chain cybersecurity requirements across critical sectors, including the financial services sector. It requires organizations to strengthen vulnerability management, incident coordination, and supplier security oversight.
NIST CSF and ISO 27036
Frameworks such as NIST CSF and ISO 27036 reinforce similar expectations by emphasizing:
Operational governance of supplier security
Transparency across technology supply chains
Resilience testing that includes vendor failure scenarios
Incident response coordination with third-party providers
These frameworks collectively signal a major shift: third-party cybersecurity is no longer a procurement function. It must now be embedded into security architecture, identity management, vulnerability monitoring, and incident response operations.
Core Technical Risk Domains in Banking.
The most effective way to assess third-party cyber risk in banking is to analyze technical failure modes within critical service domains.
Rather than relying solely on vendor categories, mature programs examine how specific technologies could fail and how those failures might impact banking operations.
Risk Area | What Can Go Wrong | What to Check |
|---|---|---|
Software Supply Chain | Vulnerable libraries, exposed secrets, tampered or unsigned releases | Secure SDLC practices, regular patching, dependency scanning, and SBOM visibility |
APIs & Open Banking | Broken access control, weak OAuth, exposed endpoints, and token misuse | API inventory, strong authentication, input validation, rate limiting, secure token usage (mTLS/DPoP) |
Access & Identity | Shared admin accounts, excessive privileges, stale sessions, and key misuse | MFA enforcement, least privilege/JIT access, session monitoring, credential rotation |
Cloud & SaaS | Over-permissioned roles, exposed storage, poor tenant isolation, weak recovery | IAM controls, encryption, data flow visibility, backup & recovery testing, logging |
Incident Response | Delayed breach notification, lack of logs, poor coordination with vendors | Defined SLAs, 24/7 contacts, shared incident playbooks, log retention, and access |
Concentration Risk | Dependency on single providers, hidden fourth parties, and single points of failure | Vendor mapping, diversification plans, exit strategies, impact (blast radius) analysis |
Fourth-Party Exposure | Hidden subcontractors, opaque hosting chains, and inherited regulatory or jurisdictional risks | Subprocessor inventory, subcontracting approval processes, and service location tracking |
Characteristics of Mature Banking TPRM Programs.
Mature banking TPRM programs prioritize vendors based on operational impact rather than contract size or procurement classification.
Key questions include:
Does the vendor support payment processing or financial settlement systems?
Does it manage customer identity or authentication processes?
Does it process sensitive financial or regulatory data?
Could this provider's failure disrupt core banking services?
Critical vendors require deeper technical validation.
Instead of relying on narrative security statements, banks increasingly request verifiable technical evidence such as:
Enforced MFA for administrative access
Detailed API permission inventories
Log retention and monitoring capabilities
Vulnerability remediation timelines
Transparency into subcontractor dependencies
Backup and disaster recovery testing results
Mature programs also extend visibility into fourth-party risks, recognizing that many banking providers rely on additional subcontractors such as cloud infrastructure providers, identity services, and payment intermediaries.
How the Genesis Platform Addresses Modern TPRM Challenges
Managing cybersecurity risk across large vendor ecosystems requires structured assessments, continuous visibility, and operational workflows to track remediation. The Genesis Platform modernizes third-party risk management by transforming traditional vendor reviews into an intelligence-driven process.
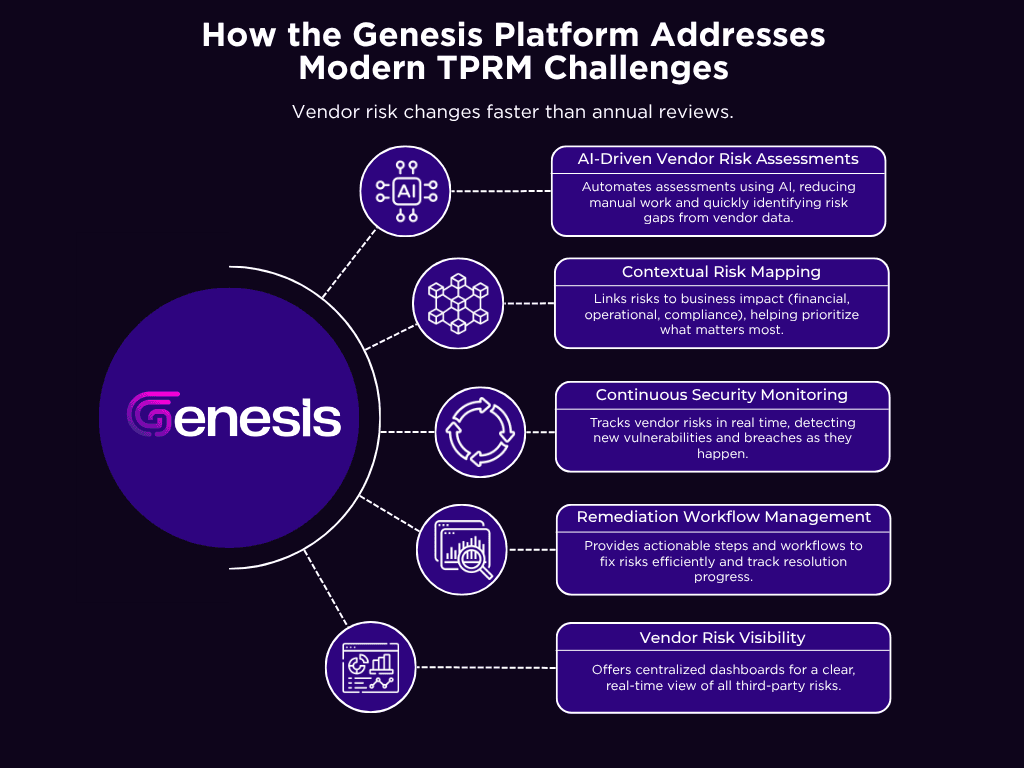
AI-Driven Vendor Risk Assessments
Genesis normalizes vendor responses and supporting evidence against established frameworks such as NIST CSF, ISO 27001, PCI DSS, and FFIEC. This allows security teams to quickly identify control gaps relevant to banking environments, including weaknesses in access control, encryption, incident response, and payment system protection.
Contextual Risk Mapping
Instead of generic risk scoring, Genesis links vendor findings to operational impact scenarios, including unauthorized transaction access, payment processing disruption, data exfiltration, and regulatory reporting failures. This helps risk teams prioritize remediation based on actual business exposure.
Continuous Vendor Security Monitoring
The platform surfaces external security signals, including newly disclosed vulnerabilities, breach disclosures, and exposed services. These indicators allow security teams to reassess vendor risk between formal assessments.
Remediation and Vendor Workflow Management
Genesis provides structured workflows for evidence requests, remediation tracking, and exception management, reducing the operational overhead that often slows TPRM programs.
Vendor Risk Visibility
Risk heatmaps and concentration views help security teams identify vendors supporting multiple critical services and detect potential shared failure points across the vendor ecosystem.